Identity and IoT – meant to be
IoT turned 21 this year. With news of its untimely “death” we should remember Identity was there at birth. In the beginning, IoT meant using Radio Frequency Identity tags for tracking fast moving consumer goods in supply chains.. Two decades on, the meaning of IoT is now using data for sense and control of smart, connected cyber-physical machines or; Connected Things. By either definition, there is an important common strategic technology that has unlocked digital transformation: Digital Twins.
Digital Twins – Everything is an API
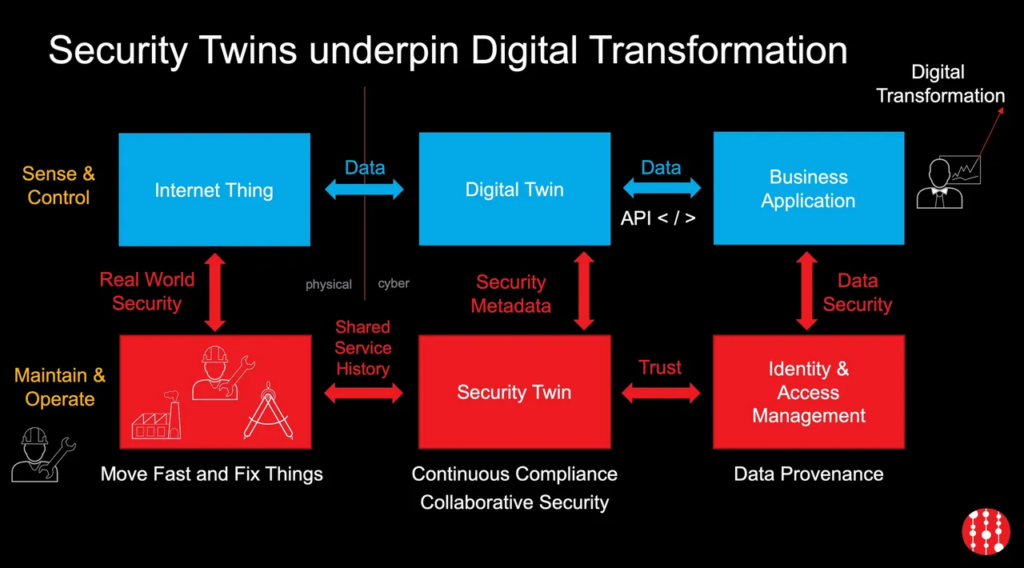
Digital twins represent real-world objects in virtual form that allow software interactions with them through data flows. Different users of Digital Twins will value data differently; a system user of a Thing places more value in live data feeds, whereas a Thing manufacturer is more interested in aggregate usage for maintenance scheduling. This indicates a need for multiple Twins.
Security Twins – the trust enabler for Digital Twins
As we move towards that world of multiple and composite Digital Twins it is important to choose and aggregate the right data sources that match your business case and take account of your risks and ambitions. Broadly these sources fall into two major categories: data from devices, and data about devices.
It’s data about devices that make up the Security Twin: maintenance information, firmware patches, configuration updates, etc. The Security Twin underpins data to ensure that connected devices are trustworthy and running in accordance with compliance processes, leaving operations and Business Intelligence software free to do what they do best: consume and analyse data from the telemetry systems unencumbered. And when moment of truth decisions must be made on live data, the vital input from a Security Twin helps chart the correct course of action.
Now it’s time to go back to what was the future of IoT: the supply chain. But this time the cybersecurity supply chain.
The Cybersecurity Supply Chain
Connected Things are only secure until they are not. Kaspersky says its ICS CERT researchers find no less than 60 vulnerabilities in ICS and IIoT products every year, and these flaws can affect hundreds or thousands of systems. If we are to move fast and fix Things, the supply-chain must collaborate; manufacturers create patches, integrators test them, owners approve, maintenance teams schedule and auditors monitor performance. The cybersecurity supply chain of a Thing is physical when installed and digital for the rest of its life. We need a way to represent that digital supply chain with Security Twins.
A Shared Service History of Things
A permanent record of when who in the supply chain did what to a Thing creates a shared service history. Just as the value of a used car is judged by its service history, the value of data from Things – and their Digital Twins – can be cross-checked against their history. Is patching history sensible? Who authorised what configurations to be loaded on the device? How long has it been running in a vulnerable state? These detailed questions are almost impossible to answer in isolation, but become clear when a collaborative maintenance system is in place.
How Do We Build a Security Twin?
An organisation will need a fast responding, secure system of record to store Security Twin information. It should store static and semi-static metadata like provisioning records, available firmware versions and issuers, X509 certs for direct methods, vulnerability reports and more. It should synchronise data of events with other supply chain participants.
Access and Governance Built on the Foundation of Security Twins
A high-quality source of security meta-information can increase visibility of risk and reduce it, while proving continual compliance at low cost. It can speed execution of operational decisions by increasing trust in data, whether those decisions are made by humans or Artificial Intelligence. Step-up authentications can be applied when it matters most, just as with human identity and access control decisions.
Governing Things to meet compliance can use the same tools used for governing human access to data. When a business is digitally transformed, everything is data, everything is accessed through APIs and unifying identity governance of Things, customers, employees and partners makes it a lot simpler to comply with regulations and improve business outcomes
Security Twins for Internet Things lower business risk.