The European Union NIS Directive represents a necessary step toward securing Critical National Infrastructure (CNI) and encouraging best practice to protect essential services. Yet there are many challenges to overcome in the next few short years before regulatory penalties start to be widely enforced. Now is a good time to start preparing.
The directive offers very little concrete guidance, other than urging CNI operators to ensure a level of security appropriate to the risk posed. The danger in providing such guidance is that complacency or misunderstanding of security would lead to thinking that check-box compliance, traditional IoT security guidelines, security certifications, one-off pen-tests or some other magic technology will provide the necessary security for ongoing operations. Unfortunately this was never really true, and in today’s fast-moving cyber world such generic point-in-time snapshot approaches to security provide little more than a false sense of security. Things are only secure until they are not. Compliance and certification need to be dynamic.
The UK joint select committee on national security strategy has discussed this at length and the realization is there – security processes must not only deal with making things secure today but how to quickly respond when they are found to be vulnerable tomorrow. An outcome-driven framework is needed that recognises security is dynamic – standards are rendered out-of-date by newly discovered vulnerabilities, one-time static evaluations of the past are not fit for purpose, yet a punitive regulatory oversight may jeopardize open and necessary collaboration to solve security issues.
Is cyber-risk insurance the answer to impending regulatory fines? What use would that be to people who need decontaminated drinking water, recovery from an electricity blackout or transportation home? And how do models for insurance cope with the connected, Linux-based world where a single bug renders a whole population of devices vulnerable all at once? Actuarial models today do not assume that every active volcano in the world could erupt at once. The reputational risk associated with cyber-physical systems is far greater than a breach of personal customer data. An apology, no matter how genuine and humble after an event, will precede many months of recovering lost trust.
Perhaps one of the biggest risks yet to be resolved with connected or otherwise ‘smart’ infrastructure is that of supply chains. The initial supply chain – sourcing, building and delivering a physical unit – is quite well understood, including so-called ‘supplier risk’ where the supplier’s suppliers are also vetted. But in Industry 4.0 the existing schemes aren’t adequate. Supply chain delivery isn’t a one-time up-front thing anymore, which can be underwritten by a static kitemark: it’s a continuous flow of updates to software, configurations, and digital IDs with deep involvement and responsibility from many suppliers and stakeholders. It’s a continuous Digital Supply Chain that lasts the life of the device.
The answer to all of this is not check-box compliance or a magical silver bullet security widget. Neither is it panic. The key here is visibility and understanding: we can be comfortable in a risk-based world and continuously exposed to new threats and vulnerabilities if we can be confident we know our level of exposure to a reasonable degree of certainty at any point in time. There are clear needs for greater visibility amongst all who collaborate on security in the supply chain, faster communication channels to resolve vulnerabilities and an ability for everyone to hold each other accountable, before regulators need step in or external alarms sound. Indeed, with more transparent sharing with regulators, there should be little need for heavy handed approaches as early warning signals could prompt remedial action before situations get out of hand. A stitch in time saves nine, as they say, and just as car insurance becomes affordable with telemetry, transparency as to how critical services are operated and maintained should lead to reductions in cyber-risk insurance premiums. And indeed cyber risk full-stop.
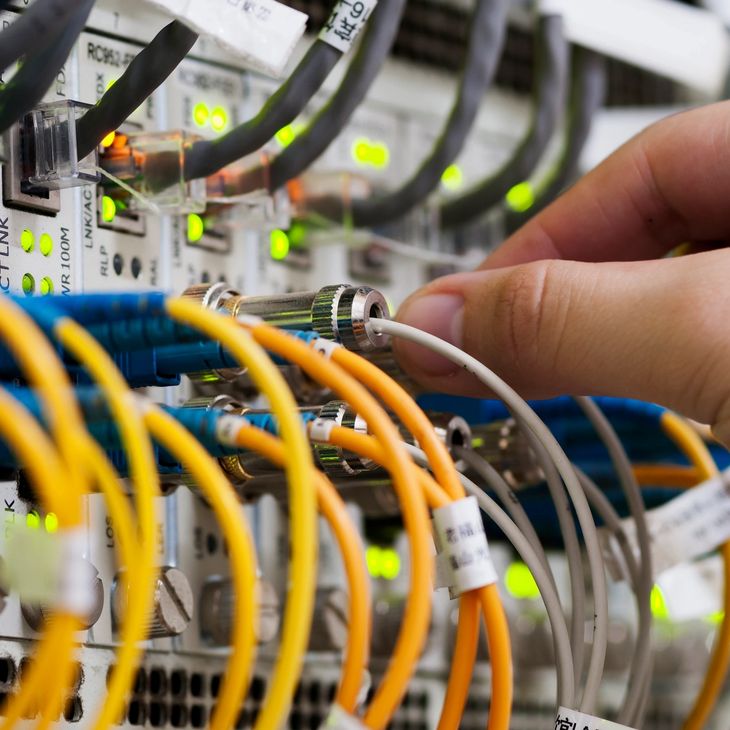
The IoT supply chain must continuously deliver security for the lifetime of devices. Distributed shared ledger technology is proving its value for cross-supply chain collaboration, and RKVST is building upon it to bring dynamic information assurance in IoT for operators of essential services.